In the midst of the fast-paced tech world, businesses often face hacking attacks, compromising on confidential information. The Distributed Denial-of-service (DDoS) falls among the most common cyber attack these days.
The DDoS involves exploit of various systems that are interconnected. Though, online security is becoming sophisticated, but hackers are eagerly looking for ways to eavesdrop on our data privacy. In this article, we are going to reveal how a business can protect itself against the rising DDoS attacks.
Make a Response Plan
When running a business, it’s essential to make a plan for the potential digital threats that could harm its online reputation. The planning should be limited to an IT team in an organization, and thus a business should involve the vendors and executive members. The plan should include the vital questions such as what would be the steps to take in case of a DDoS attack. In this way, a business will have a contingency plan and will be able to act fast at the time of any unexpected event.
Leverage the Power of Cloud Services

Cloud providers have proven to handle the data security in the best manner. According to a research, even the U.S. government opts for cloud providers due to their reliable security aspects. In addition, Amazon offers DDoS mitigation services, providing companies with cost effective DNS and secured services. The IT team in a company should search for the recent information about the mitigation services and protection against the potential cyber threats.
Include Multiple Layers of Defense
A business should stay vigilant and add layers of security into its network. In addition, the organizational departments should be provided with information about the signs to look for potential threats. Considering the fact that many businesses have started outsourcing services, it’s essential to find out if the third party implements DDoS protection. It will provide a company with more proactive approach to deal with the possible online threats.
Segmentation of IoT Devices behind the Firewall
Considering a fact that DDoS are difficult to prevent, businesses can reduce their affect by turning on the DDoS and flood protection feature in the firewall. In addition, there should be a DDoS response plan that focuses on restoration in an event of the attack, ensuring that all the IoT devices remain safe and segmented behind a firewall.
Implement a WAF
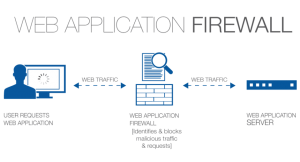
The Web Application Firewall (WAF) serves as the best defense against the DDoS attacks. It works like a strong layer of defense, blocking various malicious attacks on a website. It rests above an application at the network level, securing a server against the cyber attacks. The WAF not only provides protection against the DDoS attacks, but also enhances an application’s performance and overall users’ experience.
Educate the Employees
Awareness helps a lot when seeking for protection against the growing cyber attacks. A business can take steps to educate the employees about the dos and don’ts of a particular department that helps in protection against the potential attacks.
Considering the fact that the businesses are adapting the mobile first approach for generating revenues, it’s essential that they spread awareness about the potential cyber threats including the DDoS attack. In this way, all the employees will remain on a same page to stay safe against the DDoS attack.
Identify the Signs of DDoS Attack
Safety precaution always serves as an effective defense against DDoS attacks. Identifying a DDoS attack in the initial stages can come into handy. However, not every DDoS attacks are easy to handle. One of the reasons is that these attacks are none other than regular spike in the internet traffic.
Thus, it’s essential to spend time on the right set of training to gain expertise and identify the difference in a DDoS attack and a traffic spike. You may opt for an anti-DDoS service, and plan for an event response solution.
Use DDoS VPN
An anti DDoS VPN can conceal the real identity of a user, masking his IP address with one belonging to the VPN servers. Once a user is connected to the DDoS VPN, all the traffic is routed through the VPN provider’s servers. Being connected with the DDoS Protected Dedicated IP can safeguard a user against DDoS attacks.
ISP Provider
Falling into the victim of a DDoS attack won’t only affect you, but the ISP as well. The victim should contact the ISP in an event of the DDoS attack, asking them about the details and rerouting traffic. At the time of choosing an ISP, a user can discover if the ISP offers DDoS protection. In addition, it’s helpful to choose a backup ISP that can keep a business running perfectly at an event of DDoS attack.
In-House Protective Measures
Considering the DIY or Do It Yourself approach, a business can work itself to stay safe against the DDoS attacks. Instead of leveraging the firewalls, businesses can purchase and make use of DDoS mitigation process. These hardware is placed before the regular servers and routers, detecting and filtering the malicious traffic effectively.
What Will Happen To Business Due To A DDoS Attack?
If a DDoS attack victimizes your website, chances are that your competitor will take an edge over you through acquiring the visitors. It will negatively affect the revenues, making the visitors develop a negative perception about your business that you’re aren’t capable to secure your databases nor theirs’. Above all, a DDoS attack will keep the potential clients from reaching out to your business.
Final Words
According to a survey, companies face about 15 DDoS attacks every year and systems deal with an average offline session of about 17 hours. Interestingly, even the popular companies including GitHub and BBC aren’t safe from DDoS attacks. The tech giant Kaspersky Lab has confirmed about 40% of businesses being unclear about how to secure their online businesses against the rising DDoS attacks. Protecting businesses against DDoS is difficult, and thus this guide highlights the methods that can protect businesses against DDoS and more cyber threats.